Table of contents
Following the blog, I wrote sometime back about Packet Sniffing. We are going to implement an HTTP Sniffer In Python using Scapy.
If you are new and you don't understand what Packet Sniffing is about, please revisit that blog because it is a very good introduction. Scapy is one of the methods I had listed on Python tools.
🌟 What is Scapy?
Scapy is a powerful interactive packet manipulation program. It is able to forge or decode packets of a wide number of protocols, send them on the wire, capture them, match requests and replies, and much more.
It can easily handle most classical tasks like scanning, tracerouting, probing, unit tests, attacks or network discovery (it can replace hping, 85% of nmap, arpspoof, arp-sk, arping, tcpdump, tshark, p0f, etc.).
🌟 Implementation
Start by installing scapy and scapy.http
pip install scapy scapy.http
Define an interface handling method and I will be using Windows.
def sniff(interface):
scapy.sniff(iface=interface, store=False, prn=process_packets)
The sniff() creates a sniffing session. It also allows dissecting a flow of packets seamlessly hence traffic control.
If no interface is given, sniffing will happen on every interface eg eth0 for some Linux systems, WiFi 2 for Windows 10 etc.
The prn is the function to apply to each packet. If something is returned, it is displayed.
Now let's define the prn function;
def process_packets(packet):
if packet.haslayer(http.HTTPRequest):
url = packet[http.HTTPRequest].Host + packet[http.HTTPRequest].Path
print('URL: ' + url.decode())
if packet.haslayer(scapy.Raw):
load = packet[scapy.Raw].load
for i in words:
if i in str(load):
print('Load: ' + load.decode())
break
It takes in a packet as the parameter and analyses each packet across the network to identify or search what we are looking for below with basically a bunch of ifstatements.
packet.haslayer() is True if self has a layer that is an instance of cls (that class) hence our function depends on this to validate HTTP requests going through the network.
Then we get row data if we find what we are searching for (target words or word-list) in the traffic data.
Let's define the word lists & sniff.
words = ["password", "user", "username", "login", "pass", "Username", "Password", "User", "Email"]
sniff("WiFi 2")
The entire script;
import scapy.all as scapy
from scapy_http import http
def sniff(interface):
scapy.sniff(iface=interface, store=False, prn=process_packets)
def process_packets(packet):
if packet.haslayer(http.HTTPRequest):
url = packet[http.HTTPRequest].Host + packet[http.HTTPRequest].Path
print('URL: ' + url.decode())
if packet.haslayer(scapy.Raw):
load = packet[scapy.Raw].load
for i in words:
if i in str(load):
print('Load: ' + load.decode())
break
words = ["password", "user", "username", "login", "pass", "Username", "Password", "User", "Email"]
sniff("WiFi 2")
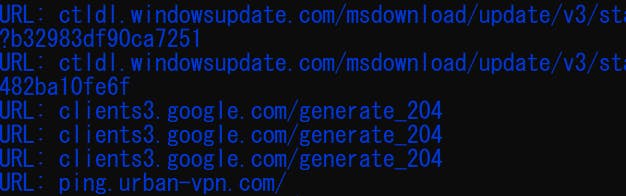
If you run the above, you would something like this;
For the full code, visit repo
🌟 Summary & Note
This is purely an educational script for basic pen-testing and troubleshooting.
Packet sniffing collects the entire packet of each network transmission. Packets that are not encrypted can be reassembled and read in their entirety. For example, intercepted packets from a user accessing a website would include the HTML and CSS of the web pages.
Network administrators use packet sniffing tools to monitor and validate network traffic, while hackers may use similar tools for nefarious purposes.
🌟 Conclusion
Once again, hope you learned something today from my little closet.
Please consider subscribing or following me for related content, especially about Tech, Python & General Programming.

You can show extra love by buying me a coffee to support this free content and I am also open to partnerships, technical writing roles, collaborations and Python-related training or roles.
📢 You can also follow me on Twitter : ♥ ♥ Waiting for you! 🙂


